The Wrike Blog
Do the best work of your life, with expert resources and all the latest Wrike news — delivered straight to your inbox.
Most popular

Try Wrike Free for 14 Days!
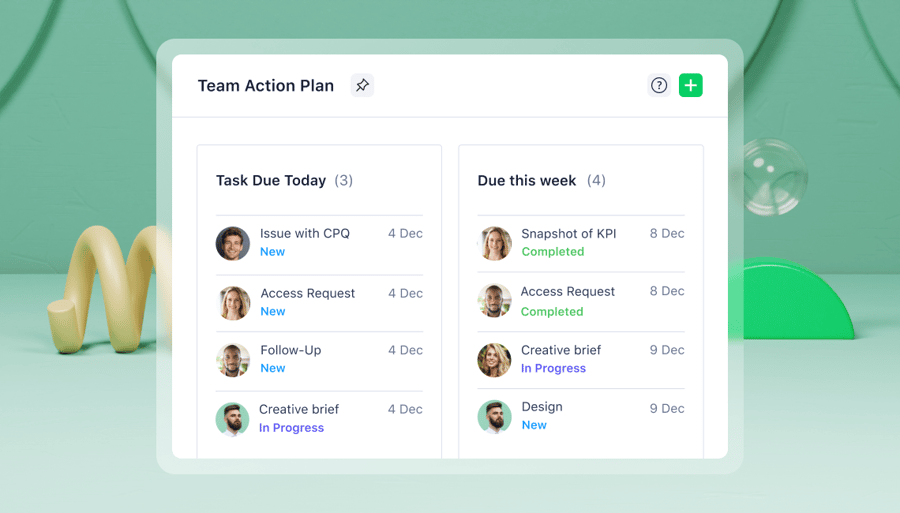
Improve your team's collaboration, enhance work visibility, and so much more.

Try Wrike Free for 14 Days!
Improve your team's collaboration, enhance work visibility, and so much more.
Get weekly updates in your inbox!

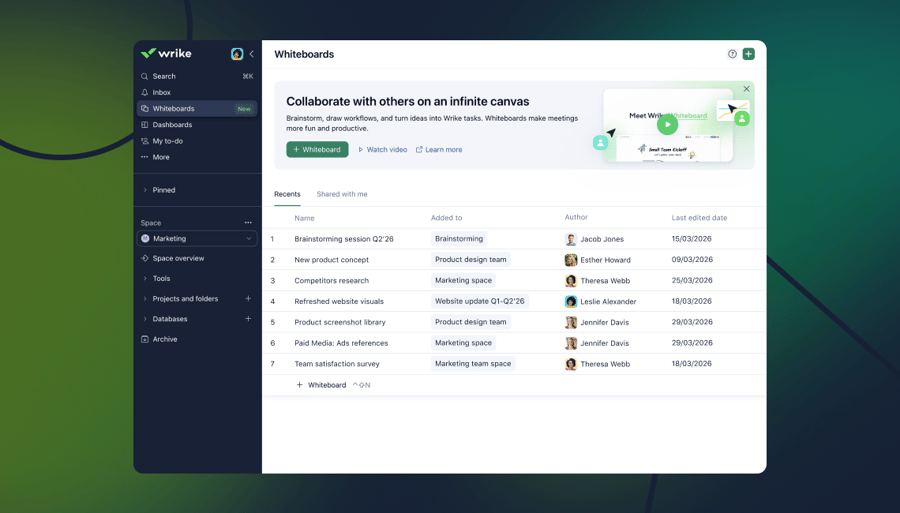
Teamwork that's faster and smarter
Ask anything about Wrike
Get instant answers about Wrike features, workflows, and use cases.
Wrike enhances its website search experience using Google's Vertex AI Search and Conversation generative AI service. Users are cautioned that generative AI might produce inappropriate, inaccurate, offensive, or unintended results, and are advised against submitting explicit, harmful, offensive, or illegal content as search input. Neither Wrike nor Google uses your search inputs to train its machine learning models or for advertising purposes, but search activities may be collected and/or stored via cookies in accordance with our Privacy Policy if you previously registered on our website. These cookies can be deleted through your browser settings. Wrike's search service is not designed to be used in connection with your personal data or any sensitive data of any kind, which users must refrain from inputting.