With the rapid increase in telecommuting due to COVID-19, cybersecurity strategies have become a greater issue for many companies. Just how prepared are organizations and their remote work security? Wrike wanted to know, so we conducted an online cybersecurity survey of 1,000+ workers employed full-time by organizations in the U.S.
Wrike’s remote work security survey
Remote statistics show that 41% of remote workers are accessing confidential work information using unsecured personal applications. This means cybercriminals could have easy access to valuable data, trade secrets, and corporate intellectual property.
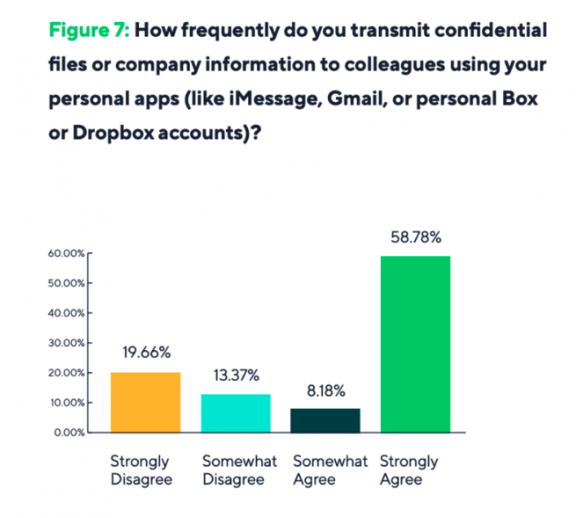
About half of these employees who use personal apps for company information say they do it every day. That means confidential information is being regularly transmitted outside of a company’s security protocols, leaving companies open and at risk of malware and breaches.
Our survey results and telecommuting statistics reveal even more about security practices adopted by companies and employees’ behaviors around those practices.
Employer remote work security strategies
Many organizations didn’t have business continuity plans as the pandemic spread, and suddenly, they had to come up with remote work and security protocols — often without an idea of how to implement or even enforce them. With that in mind, we wanted to examine security from employees’ perspectives.
- Most companies released training and guidelines for remote work
In our survey, 74% of employees report that their companies released guidelines or training for working securely while remote. However, 19.3% say they’ve received no such guidelines, which means that a significant number of employees are either unaware of their company’s remote work protocols or work for companies that haven’t created them yet.
How employees react to security strategies
One of the most vital elements of a remote work security strategy is to ensure employees understand its importance, and for the most part, we found employees do believe their companies take it seriously.
- Most workers understand common cybersecurity risks
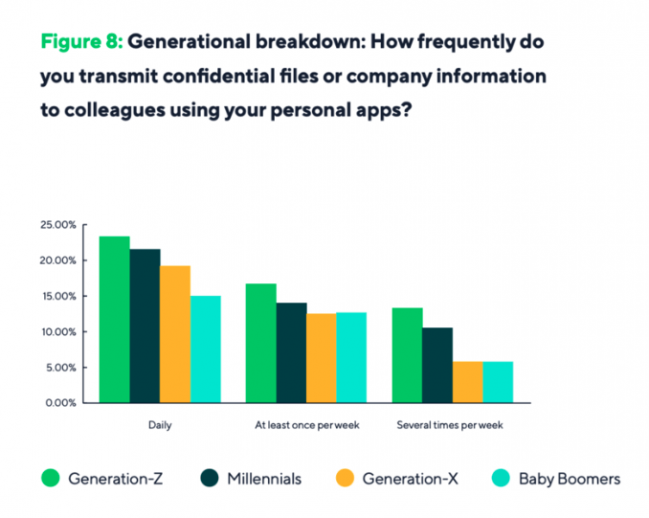
85% say they have a good understanding of cybersecurity risks and know the best practices to reduce them. - Gen Z workers are the most likely to use personal apps for work
Overall, the younger the worker, the more likely they are to use personal apps to transmit confidential information. Gen Z workers are 53% more likely than baby boomers to do so.
The importance of regular cybersecurity training
In an era where remote work is becoming the norm, cybersecurity training for employees is no longer optional, but a necessity. While technology can provide robust protection mechanisms, human error remains a significant risk factor. Phishing scams, weak passwords, and unsecured networks can all lead to data breaches.
Regular cybersecurity training can help mitigate these risks. Training should cover not only the basics of online security but also provide updates on the latest cyber threats and countermeasures. Topics could include the creation of strong, unique passwords, the dangers of using public Wi-Fi, how to identify and avoid phishing scams, and the importance of keeping software updated.
Moreover, it’s crucial to instill a culture of cybersecurity in your organization. This means that everyone, from the top executives to the newest recruits, understands their role in protecting the company’s information. Regular training sessions, reminders, and updates can help foster this culture and ensure that cybersecurity remains a top priority.
The role of multi-factor authentication in remote work security
As remote work continues to become more prevalent, so does the need for more stringent security measures. One such measure is multi-factor authentication (MFA), which adds an extra layer of protection against unauthorized access to sensitive information.
MFA requires users to provide two or more verification factors to gain access to a resource, such as an application or online account. These factors can include something they know (like a password), something they have (like a phone), and something they are (like a fingerprint).
By implementing MFA, businesses can significantly reduce the risk of a cybercriminal gaining access to their systems, even if that cybercriminal has managed to obtain a user’s password. This is because the cybercriminal would also need to bypass the second (or third) layer of authentication, which is significantly more challenging.
In addition to implementing MFA across your organization, it’s also crucial to educate employees about its importance and ensure they understand how to use it correctly. This could be incorporated into your regular cybersecurity training sessions.
Future-proofed security and the future of work
Experts believe remote work isn’t going away any time soon and might even be more common practice moving forward. That’s why it’s crucial for companies to understand cybersecurity risks why their employees are ignoring security protocols in order to future-proof remote security strategies.
- Functionality, convenience, and user experience of apps determine worker usage
Over 50% of employees say they use their own apps because their company doesn’t offer anything with similar functionality, personal apps are more convenient, or they prefer their personal app’s user experience. These factors are the top three reasons respondents are likely to bypass approved apps and use their own to collaborate with others instead.
Although workers say these are the main reasons for personal-app usage, it’s also likely that some don’t understand the security risks. External apps often request access to personal user data and malware can enter work networks with little or no record of a breach.
A secure work management solution
Overall, our survey shows that companies have been trying to be proactive about security, but there are still opportunities to improve communication around cybersecurity and to ensure workers understand the importance of preventing risks.
One of the best ways to future-proof remote work security is by adopting secure remote working tools. Wrike is dedicated to offering the most secure and reliable collaborative work management platform on the market. That’s why we offer the Wrike Lock add-on, which provides an additional layer of security by encrypting the encryption keys for Wrike workspace data (including tasks, folders, projects, workflows, and comments) and Wrike attachments with a master customer-managed key (CMK).
Download the full eBook for all of our findings. Or to see other statistics about remote work, check out our dedicated remote work statistics page.
Real World Use Cases from Wrike Power Users
We’ve compiled 6 ways creative agencies like Ogilvy-Australia and Skona use Wrike to work confidently now.
Thanks for your interest in our eBook!
Download it nowWe have also sent the eBook link to your email for your convenience.






