Key takeaways:
- What does RAID stand for? RAID stands for Risks, Assumptions, Issues, and Decisions, essential for tracking project success.
- Why is a RAID log important? It helps consolidate key project information, minimizing risks of delays, budget issues, and ensuring efficient planning.
- How can a RAID log assist project managers? RAID logs allow project managers to capture critical data, inform future projects, and optimize resource allocation.
- What distinguishes a RAID log from a risk and issue log? RAID logs are more comprehensive, encompassing risks, issues, assumptions, and decisions, while risk logs only track risks and issues.
- How can Wrike aid in managing RAID logs? Wrike centralizes RAID logs for easy access and updates, enhancing collaboration and real-time communication among team members.
One of the most critical aspects of project management is assessing and tracking the risks, assumptions, issues, and dependencies that could impact the project’s success. That’s precisely where a RAID log comes into play.
So, what is a RAID log? In this article we’re diving deep into the RAID log definition and looking at RAID log examples. We’ll also identify ways to successfully implement a RAID log in your next project.
What is a RAID log?
RAID is an acronym that stands for risks, assumptions, issues, and decisions. That’s precisely what a RAID log helps project teams identify and track during the planning and execution phases of a project.
Let’s look a little more closely at each element of the RAID log.
Risks
Risks are unexpected events that can affect your project, for better or for worse. A risk can impact anything — including people, processes, technology, and resources. Risks are distinct from issues in that issues are known ahead of time, whereas risks are events that might happen — and you might not be able to tell when.
Assumptions
The Project Management Institute defines project assumptions and constraints as “any project factor that is considered to be true, real, or certain without empirical proof or demonstration.” The problem is that it’s tough to plan a project without making some assumptions. However, you can solve this problem by identifying those assumptions at the start of the project. This is a way of putting safeguards in place in order to minimize the impact on project delivery if the assumption turns out to be false.
One variation of the RAID log calls for “actions” and “decisions” instead of “assumptions” and “dependencies.” In that version, the actions are the things that need to be accomplished in order to complete individual tasks or respond to issues, as well as the actions that are taken throughout the project. It’s also important to assign and document owners for all the actions listed in the RAID log.
Issues
Issues are problems that need consideration at the project’s outset, as well as problems you will encounter at various stages of the project lifecycle. If not properly addressed, an issue can completely derail a project and doom it to failure.
Decisions
Every decision made throughout a project should be logged and recorded to serve as a reference for teams to look at for their future projects. Details of decisions, including who made the decision, when it was implemented, and why it was made in the first place, should all be included.
In the alternate version of a RAID log, every decision that’s made throughout the project is recorded and includes the decision maker, the date and time of the decision, and the justification for the decision.
Why use a RAID log?
Keeping a RAID log is crucial because all four of its elements — risks, assumptions, issues, and dependencies — are inherent in every project. Failure to properly address these elements in the planning phase can lead to problems down the road like delays, blown deadlines, and even blown budgets.
What’s more, the RAID log serves as a great management tool that can help you consolidate information and keep the project on track. RAID logs are also helpful for assessing changes to the project conditions, optimizing effort and resource allocation, and requesting support from management and stakeholders.
What are the advantages of using a RAID log?
Using a RAID log offers plenty of advantages to project managers. RAID logs help PMs plan more efficiently, capture critical project information, and compile data that can be used to inform and improve future projects.
What are the disadvantages of using a RAID log?
One disadvantage to a RAID log is that it adds one more item to the project manager’s already heaping plate. This is why PMs must monitor their dependency on the RAID log and the amount of time spent compiling and reviewing the log to ensure it doesn’t encroach on other responsibilities.
Is a RAID log the same as a risk and issue log?
RAID logs are inherently more comprehensive than risk and issue logs. RAID logs capture the same information — risks and issues — plus assumptions and decisions, which give a more well-rounded view of the project than risk and issue logs can.
Example of a RAID log
Here’s a visual RAID log example:
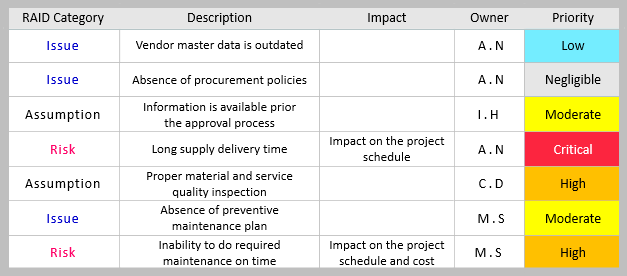
This example keeps it pretty simple, but the project manager can decide the level of detail each item in the log will have.
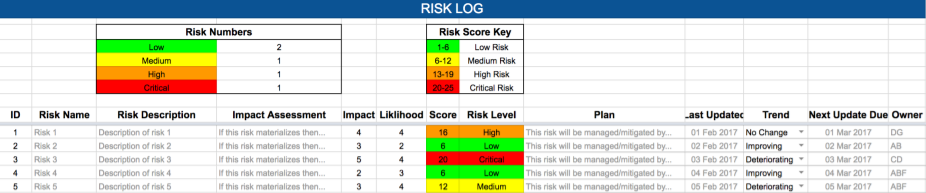
Alternatively, you can break out each category of the log into its own tab, section, or standalone document. Here’s a risk section from another RAID log example that’s much more detailed:
How to implement a RAID log
As you can see from the examples above, you can set up a RAID log using a simple spreadsheet. Each element of the RAID log can have its own tab, or you can put everything together on the same tab for smaller, less complex projects.
When it comes to maintaining the RAID log, the PM doesn’t have to be the only one inputting new data. Team members, project sponsors, managers, partners, and other stakeholders may all be able to access, update, and review the RAID log to help relieve some of the load from the project manager and ensure that critical RAID info doesn’t fall through the cracks.
How Wrike can help with your RAID logs
With Wrike, you’ll be able to store your RAID logs in one centralized location, making it simple for all vested parties to access and update the log. What’s more, you’ll be able to communicate with your colleagues and get real-time responses on revisions to the RAID log.
Want to see all the ways Wrike can help you implement RAID logs and streamline project management at your organization? Get started with a free two-week trial today!